Web Application Pentesting
About Course
“Do Not Use The Knowledge and Information from this Course for Unethical Purpose”.
Cybersecurity has become the prime concern for every service organization these days. Organizations, unacquainted with the cyber-attacks and the harm it can cause to the systems are falling prey to these attacks. Therefore, the most appropriate way to secure the organization is to focus on comprehensive security testing techniques. The effective testing approach to assess the current security posture of the system is known as penetration testing also known as ‘Pen Testing’.
Web application pentesting must be conducted by organizations and individuals with web apps periodically to keep up with the latest attacks methodologies and security flaws. With the rise in web-based applications, huge amounts of data are stored and transmitted through them, making them attractive targets for cyber attackers.
Web app penetration testing is the process of simulating hacker-style attacks to identify potential vulnerabilities in web apps using simulated attacks. Its purpose is to uncover and mitigate security risks to improve the application’s overall security posture before they can be exploited by real-world attackers.
It is essential as it helps in determining the security posture of the entire web application including the database, back-end network, etc. Moreover, it suggests ways to strengthen it.
A career as a pen tester gives you the opportunity to apply your hacking skills for the greater good by helping organizations protect themselves from cyber criminals. It’s also an in-demand, high-paying career path.
According to Glassdoor, the estimated total pay for penetration testers in the US is $97,638 annually. This figure includes an average base salary of $90,673 and $6,965 additional pay. Additional pay may represent profit-sharing, commissions, or bonuses.
Course By – “The Cyber Mentor”
Course Content
All Lessons
-
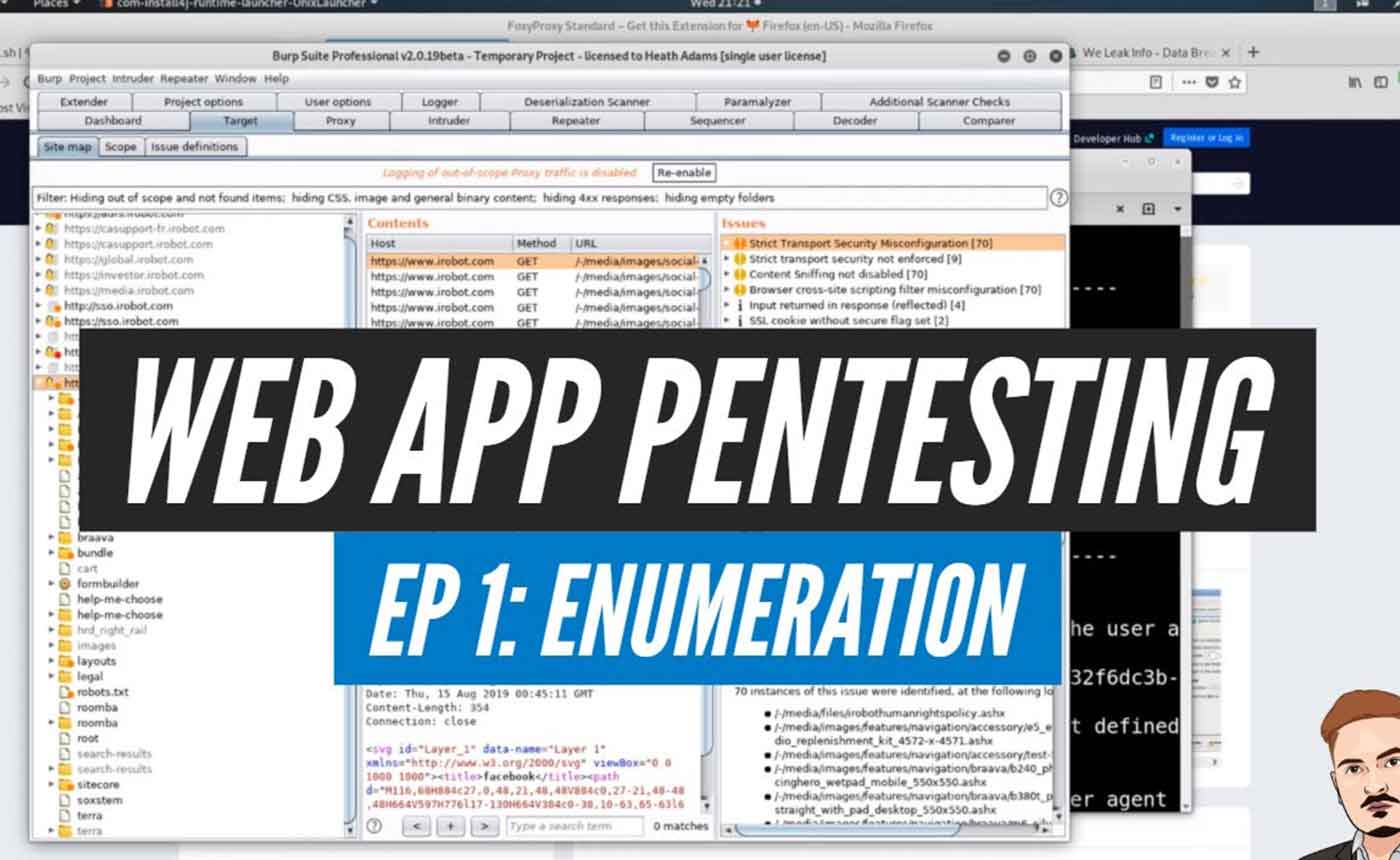
Episode 1 – Enumeration
02:33:43 -
Episode 2 – Enumeration, XSS, and UI Bypassing
01:02:51 -
Episode 3 – XSS, SQL Injection, and Broken Access Control
01:32:31 -
Episode 4 – XXE, Input Validation, Broken Access Control, and More XSS
01:57:15 -
Episode 5: SQL Injections and Live Bug Bounty Hunting
02:52:08 -
Bug Bounty – Hunting Third Level Domains
59:45 -
Burp Suite Pro Walkthrough
18:08 -
Broken Object Level Authorization (BOLA) Explained
08:06 -
HTTP Fundamentals in 10 Minutes
10:34 -
Learn WebApp Pentesting: 2023 edition
08:09 -
Top 3 Programming Languages for Cybersecurity in 2023
07:38 -
Learn Offensive JavaScript TODAY
12:32 -
Clickjacking – Hacking Web Application UIs
08:01 -
New Web Hacking Tool That May Replace Burp Suite
11:40 -
Blind SQL Injection Made Easy
11:39 -
How to Hack WordPress
14:06 -
Directory Traversal attacks are scary easy
09:41 -
Web App Hacking with Caido.io
01:57:48
Student Ratings & Reviews
